WooCommerce Vulnerability of July 2021: What is it exactly and how do I fix it?
kraftpixel-admin
WordPress WooCommerce Critical Vulnerability of July 2021
What it is exactly in the code and how do I fix it?
On 13th July 2021, WooCommerce began alerting the plugin’s users about a critical vulnerability. It is so critical that WooCommerce is forcing users to update and has requested all WooCommerce users to check if they are updated. However, a big challenge lies in front of WooCommerce because it can only reach out to WooCommerce users whose email addresses they have which means millions of site owners are going to be left unaware and open to an attack that exploits this vulnerability. It is quite frustrating to know that. Such a security vulnerability in our experience of WooCommerce is quite rare.
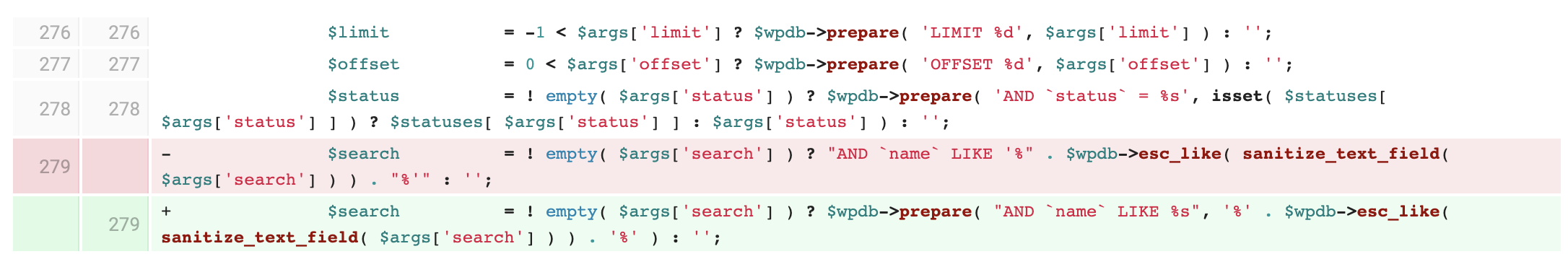
In our experience, from what we have seen, the vulnerability is quite critical because this is an Unauthenticated SQL Injection (SQLi) vulnerability affecting WordPress WooCommerce plugin version <= 5.5.0 and here is a glimpse of what the patch fix targets. After inspecting the older and patched WooCommerce versions it looks like the patch fixes the vulnerability here in this file — wp-content/plugins/woocommerce/includes/data-stores/class-wc-webhook-data-store.php:
How do I fix the WooCommerce Vulnerability?
You can be happy that the team over at WooCommerce has brought out the patch fix. Follow the official steps out here and if you are still struggling, reach out to us and we will help you out with this at our standard professional fees.
If you are worried about updating to the latest WooCommerce 5.5.1 due to compatibility issues with your current theme and other plugins, generally we would recommend you to update to the closest patched WooCommerce version, which for example, would be WooCommerce version 4.9.3 if you were currently on WooCommerce version 4.9.2.
We have sourced the following table from the official source and added links to the patched versions from the official WordPress Plugin repository so that it might help some of the users download the older patched versions of WooCommerce and the blocks plugin.
| Patched WooCommerce versions | Patched WooCommerce Blocks versions |
|---|---|
| 3.3.6 | 2.5.16 |
| 3.4.8 | 2.6.2 |
| 3.5.9 | 2.7.2 |
| 3.6.6 | 2.8.1 |
| 3.7.2 | 2.9.1 |
| 3.8.2 | 3.0.1 |
| 3.9.4 | 3.1.1 |
| 4.0.2 | 3.2.1 |
| 4.1.2 | 3.3.1 |
| 4.2.3 | 3.4.1 |
| 4.3.4 | 3.5.1 |
| 4.4.2 | 3.6.1 |
| 4.5.3 | 3.7.2 |
| 4.6.3 | 3.8.1 |
| 4.7.2 | 3.9.1 |
| 4.8.1 | 4.0.1 |
| 4.9.3 | 4.1.1 |
| 5.0.1 | 4.2.1 |
| 5.1.1 | 4.3.1 |
| 5.2.3 | 4.4.3 |
| 5.3.1 | 4.5.3 |
| 5.4.2 | 4.6.1 |
| 5.5.1 | 4.7.1 |
| 4.8.1 | |
| 4.9.2 | |
| 5.0.1 | |
| 5.1.1 | |
| 5.2.1 | |
| 5.3.2 | |
| 5.4.1 | |
| 5.5.1 |
Have you made the fix in your WooCommerce website? Start a discussion in the comments.